Carol takes us on a tour of the security-related parts of the updated Navigator for i interface, which IBM shipped in the latest Technology Refreshes for IBM i V7R3 and V7R4.
Start the celebration! We now have a new Navigator for i interface to help us manage our systems, including managing security! The interface is available as part of the most recent announcement: V7R3 TR11 and V7R4 TR5. You can find information on the new V7R3 TR11 features here and V7R4 TR5 features here. But let’s take a closer look at some of the security-related features.
Accessing New Nav and Its Features
You can launch “New Nav” (as it’s fondly called) via the URL http://your-system-name:2002/Navigator/login. The New Nav interface isn’t (yet) the default because, while most functionality of the Heritage Nav (the politically correct term for the current, old, and quite frankly ugly interface) has been brought over, the transfer isn’t yet complete. Give it another six months (or so) and I’m guessing IBM will switch the default to New Nav. In the meantime, the features of New Nav are so cool and easy to use that you really need to give it a try. Then simply bookmark the URL to use New Nav until the default is switched.
Security-Relevant System Values
One of the first things you’ll notice about New Nav is that you navigate via icons rather than words. To see all system values, float your cursor over the clipboard icon and then click on System Values. A list of system value categories is displayed. In Figure 1, I clicked on the Auditing category. From this window, I can manage all QAUD* system values. One of the things I like about New Nav is the way it relates the values shown with the corresponding values in the greenscreen, which is incredibly helpful if you’re moving between the two interfaces.
Figure 1: Navigate via icons rather than words.
User and Group Profiles
Float down to the people icon and you can choose to create a new user or group or work with a list of user profiles or group profiles (see Figure 2).
Figure 2: Work with Users and Groups.
The list functions are incredibly more useful than the corresponding feature in Heritage Nav. In Heritage Nav, the list of users was very difficult to search through, and the only fields provided were the profile name and description. In New Nav, a default set of profile attributes are displayed, but if you don’t like what we (the set of advisors that had input into the look, feel, and functionality of New Nav) chose, no worries; simply click on the vertical dots in the upper right corner of the window (see Figure 3) and you can reorder what’s there or add or remove attributes to make it work for you. In addition, you can filter user profiles—not only by name (which barely worked in Heritage Nav)—but also by any attribute displayed. If you get a filter that you want to save or perhaps even run via Run SQL Scripts or put into a CL, you can click on “SQL” in the upper right and the SQL will be displayed. So handy!
Security
The padlock icon has appropriately been assigned to the Security category. The Security category is one of the categories has been “cleaned up” from Heritage Nav. Out-of-date features have been removed and several features added. For example, Single Sign-On configuration has been consolidated into this category rather than being spread between the Security and Network categories. Better yet, the EIM and Network Authentication Service functions have been totally reworked, hopefully making them easier to use and removing some of the bugs. A link to the new Digital Configuration Manager (DCM) interface has been added. (Did you even know there was an updated interface for DCM that’s been available for well over a year? If not, you’ll definitely want to give it a try the next time you have to work with digital certificates.) Another addition is the Security Configuration Information view. It’s a consolidation of the values from displaying the security-relevant system values (DSPSYSVAL *SEC), Display Security Attributes (DSPSECA), and Display Security Auditing (DSPSECAUD), and it makes use of the QSYS2.SECURITY_INFO IBM i Service. See Figure 3.
Figure 3: Security Configuration consolidates DSPSYSVAL *SEC, DSPSECA, and DSPSECAUD.
Application Administration Is Now Function Usage
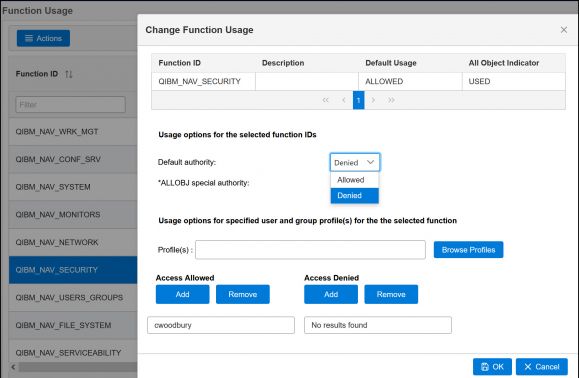
Another feature that has a totally new look and feel is known as Application Administration in Heritage Nav but as Function Usage in the Security category in New Nav. Why the rename? Application Administration may have sounded better, but once you understand the feature, it really has no meaning. Function Usage, while it may not be obvious, at least has a correlation to the CL command Work with Function Usage (WRKFCNUSG), which allows you to manage this feature in the greenscreen. See my previous articles for a description of Application Administration/Function Usage. Even though the interface has changed, the reasons for using it have not.
I’ll admit that when I first looked at this feature in New Nav, it took me several minutes to get used to it because I was used to the tree structure in Heritage Nav. But after I started to utilize the sorting and filtering features, it started to make sense. What also helped was better terminology. To me, the terminology used in New Nav to implement the various features makes more sense. For example, Figure 4 shows the window shown when you highlight a function, right-click, and choose Change. To me, it’s much more obvious that you can choose “Denied” for the Default authority rather than checking or unchecking the selection as in Heritage Nav.
Figure 4: In New Nav, it’s easy to change the default action of a function.
Another term that caused some confusion in Heritage Nav was “Customize,” meaning that you want to allow or deny specific users or groups. Instead, now you’ll see a column entitled “Profiles Allowed/Denied” with the value of either NO or YES. If NO, well, hopefully it’s obvious. No users or groups have been allowed or denied specific access to this function. If YES, well then…they have! You can click on the function and choose Change to see or change what’s been previously specified.
Finally, to change more than one function at a time, simply highlight multiple functions prior to right-clicking and choose Change. One important thing to be aware of: Many of you have used Application Administration/Function Usage to control which parts of Navigator for i users, especially end users, can see. Those settings do not apply to New Nav! That’s because, as I’ve explained, some features have moved categories, new features have been introduced, and others have been consolidated. In other words, there was no way to accurately translate the settings of Heritage Navigator for i categories into New Navigator for i categories. The good news is that you can allow/disallow usage by category and not have to go into individual functions to apply the settings as you did with Heritage Nav. And, as I just discussed, you can highlight multiple functions and change them all at once. So while you’ll need to go in and customize the QIBM_NAV_* functions to control which categories users can see in New Nav, it should be a simple task.
Not Quite All There, But That’s OK
Once you start to use New Nav, you’ll notice that some features haven’t (yet) made it into New Nav. For example, in the Security category, features not yet brought over include the ability to change permissions on objects, create authorization lists and change their permissions (although you can display the permissions along with the objects secured by the lists), and configure the Intrusion Detection feature of IBM i. You’ll also find that the file share feature of the File System category has been brought into New Nav, but the rest of the file system features have not. However, the file shares feature on its own is worth a look. It includes two new features: an indication of whether the path assigned to the share exists and the ability to specify that an encrypted session is required (an attribute not externalized in Heritage Nav). But don’t worry! It’s not like this is the first and only version of New Nav to be released. Why didn’t IBM wait until all features were available? Because they, along with the technical advisors who have been using New Nav, felt that there was so much value to the new interface that it was better to release what’s already available so everyone (rather than just a few of us) could start to use this new and improved interface.
Audit Journal Entry Table Functions
I would be remiss if I didn’t mention another feature in the latest Technology Refresh—that is, the addition of seven new table functions that parse out the entry-specific portions for audit journal entries. In addition to the four introduced in the previous Technology Refresh, we can now use SQL to parse out the CD, CO, CP, DO, EV, GR, and SV audit journal entry types. I explain how to use these table functions here. Thanks, once again, to Scott Forstie and team for making the ability to get information out of the audit journal so much easier.
Summary
Yes, a handful of features haven’t yet been brought over to New Nav. But features from all categories are in New Nav, and most are far and away superior to Heritage Nav. I encourage you to give New Nav a try and see for yourself. To make sure you get the PTFs you need to take New Nav for a spin, click here.



















 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online