Simplify the way you ensure that IBM i system values are in compliance.
Hopefully, you reviewed and configured your System i server's system values as part of your security procedures. If not, you should take the time to familiarize yourself with these values to understand how they impact security. With each new release of the operating system, IBM adds more system values (information about new values is available in the "Memo to Users" at the online Information Center). And once these values are set, you must ensure they stay that way. But manually comparing values is both labor?intensive and error?prone. There are better approaches.
IBM Lockdown
Starting with V5R2 of the operating system, IBM i includes the ability to lock selected system values using System Service Tools (SST). This lockdown prevents even the most powerful users from making changes. However, many people won't use this feature because they aren't comfortable with the SST interface and are afraid they won't be able to unlock these values later.
Compliance Monitor
Compliance Monitor, the leading IBM i audit forensics and report solution from PowerTech, offers two ways to help with this process:
Event Monitoring
If you are auditing *SECURITY events in the audit journal, modifying any system value causes an SV event to be written. Compliance Monitor can report the details of those events, including information about the value change and the user who initiated the change. And if a value is changed and then returned to its original value, Compliance Monitor registers two separate change events.
Scorecard Analysis
Compliance Monitor's System Scorecard (see Figure 1) provides a rapid, point-in-time compliance check of key system values against policy. System values are graded using a weighted scale that you can specify in order to create an overall compliance rating. You can use its Best Practices policy to determine whether a system is well-configured and its Policy Editor to customize the policy for special requirements. Compliance Monitor performs its analysis and presents an easy-to-read dashboard report that you can use to prove compliance to auditors or to highlight policy discrepancies that need to be fixed.
Figure 1: This sample System Values Scorecard shows you at a glance whether you're in compliance. (Click images to enlarge.)
Compliance Monitor's unique architecture lets you apply a centralized policy to any number of end-point reporting systems, or each end-point can have a custom policy (Figure 2). For example, all production partitions could use one central policy, while each development and test partition has its own policy. And international organizations can use different policies based on each country's requirements and regulations.
Figure 2: Compliance Monitor's integrated policy editor allows customization of security policies throughout the organization.
You can define system value requirements with flexibility. After you select the system value you want to review (Figure 3), you can specify whether a certain setting is allowed, disallowed, or required. Then, you can define both a severity and the penalty to assess during the analysis if the value becomes non-compliant. Finally, if a system value should not be included in the review, you can select Allow any value and the attribute settings are ignored.
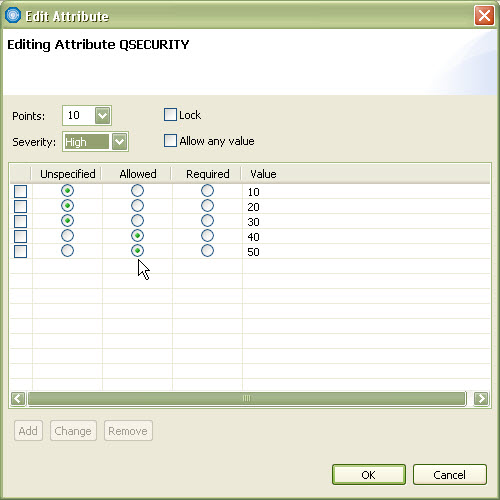
Figure 3: Policy settings for QSECURITY system value or any other system value are flexible.
You can export and import policies between systems for easy administration. And the policy editor lets you access normal system values and other attributes, such as whether changes are allowed to security system values.
Real-Time Alerting
If you want to be notified when a system value is modified, you can use PowerTech Interact for real-time alerts of activities, including QAUDJRN events. With Interact, you can communicate with enterprise monitoring solutions and escalate events to cell phones or email with powerful tools like Robot/CONSOLE and Robot/ALERT.
Working Together
To keep your system secure and compliant, you need to work with IBM i security controls to set your system values properly and then ensure they remain in compliance. PowerTech's Compliance Monitor and Interact bring together event monitoring, scorecard analysis, and real-time alerts for a complete security compliance solution.




















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online