June 16, 2023
June 16, 2023 | Volume 14 Issue 83
- LEAD ARTICLE: Open Source Starter Guide for IBM i Developers: Language Basics
- FEATURED VIDEO: A Moment with Carol Woodbury: Taking the Mystery Out of Group Profiles
- FEATURED NEWS: IBM to Grant $5 Million In-Kind for Schools to Boost Cybersecurity, Together with Enhanced Skilling on AI
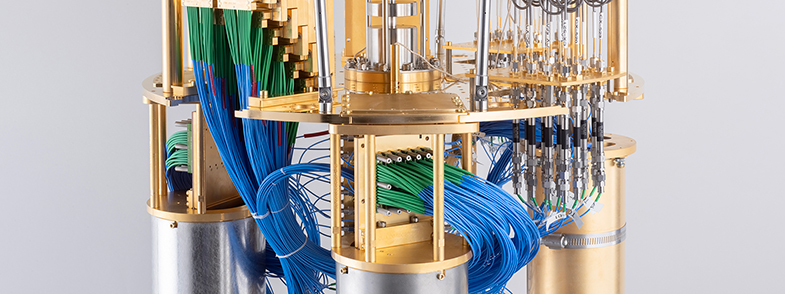
- NEWS HIGHLIGHT: IBM Launches $100 Million Partnership with Global Universities to Develop Novel Technologies Towards a 100,000-Qubit Quantum-Centric Supercomputer
- WHITE PAPER DOWNLOAD: Profound Logic Solution Guide
- WEBCAST LEARNING: Low Code: A Digital Transformation of Supply Chain and Logistics
- UPCOMING EVENT: OCEAN TechCon23 - July 27 - 29, 2023
Open Source Starter Guide for IBM i Developers: Language Basics
I don’t plan to spend a lot of time in the minutiae of the Ruby language. The goal of this series is to give you enough to go on to get started.
By Pete Helgren
Editor's Note: This article is excerpted from chapter 6 of Open Source Starter Guide for IBM i Developers, by Pete Helgren.
And although Ruby is based on POLA, there is enough “surprise!” in the way things work that it is worthwhile to go over some of the basic things and at least point out where I got either derailed or stumped. Sometimes, Grasshopper, all you need is a little enlightenment!
IBM Quantum Computer Demonstrates Next Step Towards Moving Beyond Classical Supercomputing

IBM to Grant $5 Million In-Kind for Schools to Boost Cybersecurity, Together with Enhanced Skilling on AI
With cyberattacks on the rise across schools, IBM Education Security Preparedness Grants have already benefited more than 350,000 students globally
Now in its third year, grants are expanding to offer students and teachers access to cyber and AI skills through IBM SkillsBuild
By IBM Systems
In response to the growing threat of ransomware attacks against schools around the world, IBM (NYSE: IBM) today announced it will provide in-kind grants valued at $5 million to help address cybersecurity resiliency in schools. Since its creation in 2021, the IBM Education Security Preparedness Grants program has expanded globally, and this year will also include enhanced offerings from IBM SkillsBuild on topics including AI and cybersecurity.
|
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. Get your copy of this important guide today! Download your copy today! |
|
Supply Chain is becoming increasingly complex and unpredictable. From raw materials for manufacturing to food supply chains, the journey from source to production to delivery to consumers is marred with inefficiencies, manual processes, shortages, recalls, counterfeits, and scandals.
Watch Now. |
A Moment with Carol Woodbury: Taking the Mystery Out of Group Profiles
Group profiles help with role-based access on the IBM i.
By Carol Woodbury
Join Carol in this video to understand a bit more about group profiles and how you can use them to implement role-based access on your IBM i. She illustrates how you can take advantage of group profiles in your organization to help quickly grant proper authorities for roles.
Want to learn more about the benefits of Pen Testing your IBM i? Contact us today at www.dxrsecurity.com























 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn: