Are you taking IBM i security for granted? Don’t let ignorance be your security policy.
By Pauline Brazil Ayala
IBM i has the great potential of keeping your data secure at the highest level, but is it configured to take advantage of all the security features the system provides? With the prevalence of cyberthreats in today’s market, neglecting IBM i in an organization’s security policy poses major risks. The data stored on the system and the business processes running on it are highly valuable and require just as much or more security focus as your Windows and Linux servers. Let’s look at four major system areas and examine why you should pay attention to the unique facets of the IBM i to keep your critical assets safe from intruders.
#1: Resource Security
It is no surprise to anyone that ransomware is a huge threat in the cybersecurity space. The number of incidents is staggering, the results are devastating, and there is no sign of it slowing down. For some, however, it is still a surprise that the IBM i needs protection from ransomware. Left misconfigured, the potential for the Integrated File System (IFS) to be corrupted is a real threat. The IFS can be best likened to a UNIX file system and is where all modern applications reside on the IBM i. In the past decade, there have been considerable advancements on the IBM i platform, especially in the area of open-source technology and the PASE environment, which has led to increased usage of the IFS. Consequently, it is more critical than ever to be aware of your IFS security and ensure it is included in your security policy considerations.
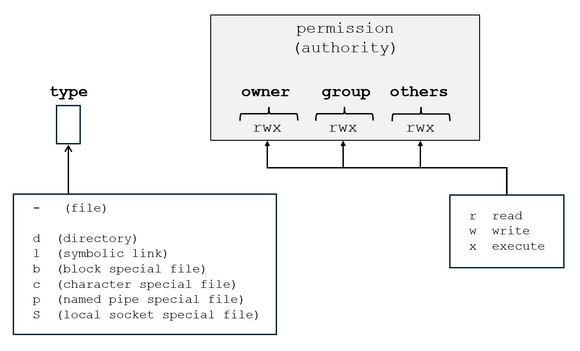
The default permissions granted to an IFS object are RWX (read, write, execute), which effectively grants all users unrestricted access to the object, as illustrated in Figure 1. Often when data or applications are loaded onto the IFS, they are done so with default permissions.
Figure 1: Default permissions of RWX (read, write, execute) are granted to the owner, the group, and the public for IFS objects.
With critical modern applications residing on the IFS, if you do not take the time to secure this file system properly, these applications and data can easily be accessed by anybody, including malicious actors, which can lead to data corruption, covert object replacement, unauthorized permission changes, and data exfiltration, among others. This is the area of the system that can house viruses and ransomware, so it is very important to understand how your IFS is being used and reduce the access granted to users as much as possible.
#2: Network Security
With the exponential rise in security incidents over the past several years, perimeter security has become widely regarded to be insufficient as a singular form of protection for a corporate network. Although firewalls are a good first-level check for the traffic that passes through them, they are often bypassed when other means of network penetration are used (e.g., phishing emails). The move toward zero-trust environments is highly recommended to enforce proper access controls down to the asset level and to prevent lateral movement within a network in case of a breach. If malware infects some part of your network, this helps contain it and prevent it from spreading.
On IBM i, many remote servers (e.g., FTP, ODBC/JDBC, SQL, File Server, Telnet, etc.) are turned on by default and can allow users with legitimate system access the ability to bypass their usual application-level security and access whatever they want by using the remote service. In addition to these default services, out of the box, there are no monitoring/auditing capabilities in place when these remote servers are accessed. PASE applications that come in directly through socket connections at the port level also go unmonitored and are not audited by default. All ports to the system are open as well, unless you have a solution in place to block specific ports.
Given the typically critical nature of IBM i servers, it is important to monitor and secure network traffic directly to the IBM i. Exit point security helps with this. The IBM i has a unique registration facility that lets you do additional processing on all remote access to the system (albeit through coding or investing in a software package) so that you can perform granular level tracking to see details on all transactions happening within your network as well as put controls in place to allow only authorized traffic, unlike a firewall where you only see the connections happening. To reduce the threat factor on the system, end those remote servers that do not serve a business purpose. Additionally, change your system configuration so that those servers no longer start automatically.
#3: User Profiles (Accounts)
Compromising privileged users is the most common means used by novice hackers and in phishing attacks to gain access to sensitive data. This should not be taken lightly, because the incidence of attacks has risen greatly since the availability of Ransomware as a Service (RaaS) and GenAI, which lower the skillsets needed to conduct a cyberattack. It is imperative that you take measures to safeguard the user profiles on all of your systems. This can be achieved with the following:
- Implementing the least-privilege model: Having numerous privileged users on a system increases the threat factor on the system because of the increased probability and potential damage caused by a breach. Reducing the privileged accounts to a minimum should be a top priority. Privilege escalation tools can be leveraged to cover the gap in running essential privileged operations.
- Strong password policies: Advancements in AI and quantum computing will decrease the time required to break passwords using brute force attacks in the coming years; therefore, it is critical to maximize password complexity.
- Multi-factor authentication (MFA): MFA is another layer of protection that can help prevent fraudulent access of user profiles. Although sophisticated attacks may be able to easily bypass MFA, common phishing attacks can be stopped with MFA in place.
- Profile usage policies: Retaining user profiles that are enabled but not in use increases the threat factor on a system, and keeping profiles of former employees poses an even bigger threat of unauthorized access being gained. With key stakeholders in your company, determine the appropriate period of inactivity time acceptable for your business and regularly monitor users to be disabled and deleted. There should be a multi-department process in place to include deprovisioning users when an employee leaves the company.
#4: System Configuration
The IBM i is well known for its secure architecture, but do not assume the default configuration is a secure configuration. Take advantage of security-related system values that are provided with the operating system to harden your server before deploying it into a production environment.
The IBM i comes equipped with highly secure auditing technology, but it must be enabled to reap its benefits. Other platforms provide logging features, but these can often be altered since the log data is stored in simple text files. Conversely, when log data is entered in IBM i’s security audit journal, there is no way for it to be tampered with.
Without auditing configured, there is no way to perform forensic research on a system should a breach be suspected. Many people claim their IBM i has never had a security breach, but without auditing in place and being monitored, there is really no way to validate that claim or confirm any suspicions.
In today’s cyber climate, it has become the norm for the general public to expect security measures to be in place to protect the data you have gathered about them. Indeed, there are many regulations that apply to general online security practices as well as industry-specific criteria where compliance must be achieved. But even without the requirements of regulatory compliance, in the case of a security breach, an organization is faced with a lot of pressure to retain or regain trust and reputation in the sight of the customer base, not to mention the obvious financial hardship that can ensue.
It's a Good Start
While this is not an exhaustive list of all the security components that affect IBM i, paying attention to these major areas and incorporating them into your security strategy will greatly improve the protection of your IBM i business assets.













 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online