Having proper policies and procedures in place is the key to maintaining user profiles.
An audit of your IBM i security can be stressful—people coming in and looking at your policies and procedures for how you maintain the security on your system. This doesn’t need to be a time of anxiety. I actually love being audited. Or as I call it “Audit Season.” Not only am I able to show off how well my system is being secured, but I try to impart a little knowledge to the auditor on how IBM i security works its magic. Since I’m probably in the minority for liking audits, let’s discuss one thing that can be done to make your audit a little easier.
My biggest pet peeve is having old, unused user profiles on the system. Someone may have decided a long time ago to leave them because it’s too big a hassle to remove them or you may not know where to begin. Think of user profiles as socks in a sock drawer. You’re looking for a particular sock, but there are hundreds of socks in this drawer. Wrong size, wrong color, socks with too many holes…it can be frustrating, especially if you’re running late for work. But you must search through all of the socks to find the ones you’re looking for. Wouldn’t it be easier and faster if the sock drawer contained only socks that were useful to you?
In my opinion, having proper policies and procedures in place is the key to maintaining user profiles. More than likely, every company has a policy when creating new user profiles. What department the user belongs to will determine what type of profile is created. What the user’s job functions are will assist with determining what third-party applications they will need access to. These are some of the same things you will need to consider when creating/modifying your user profile deletion policy.
So, what do you need to look at when deleting profiles? One thing that I’ve found helpful in determining which profiles need to be deleted is a weekly termination list from Human Resources. This type of report should contain the following: first name, last name, user ID (if possible), department, and the last date of employment. You could get creative in your policy and state that with this report the user profile associated with the employee is disabled on the system. Then, after waiting a certain period of time to make sure the profile is truly not needed, say a week, it can be deleted.
This method could work even if you’re not able to receive a report from Human Resources. If you’re unable to get this type of report, then as an addition to your user profile deletion policy, an agreement needs to be made on how long a user profile can sit on the system with no activity against it. In my experience, I have seen 60 days of inactivity as the most common length of time. This, of course, is all based on your environment and company needs. However, determining how long a user profile has been inactive on a system can be a little tricky. There are several date field parameters in a user profile, so you must look at more than one in order to make your decision. By using the Display User Profile (DSPURSPRF) command, you can send the output to a database file and then use a query to lay out the fields of interest. One of the first date parameters to look at will be the Previous Sign-on date. This date is the one modified when a user connects to the system by a 5250 emulation such as Reflections or Client Access. The other date parameter is the Last Used date. This one reflects usage through other means. For example, a user has a drive mapped to the IFS, where they access files but don’t necessarily sign on to the system.
OK, so now you have a list of profiles that have not been used in the last 60 days. What’s next? Now you look to see what kind of user profile it is. I generally break user profiles up into several categories. After all, not every profile is assigned to the general user community. Here are the categories that I use:
- User
- Help Desk
- Computer Operations
- Developer
- System Administrators
- Service Profiles
- FTP Profiles
- Third-Party Application Profiles
- Group Profiles
- IBM-Supplied Profiles
The first five categories on the list are likely to show up on a termination report, so the 60-day policy would most likely apply to those. Of course, with every policy there are always exceptions. Here’s how I define the last five categories:
- Service Profiles—Profiles used for internal services. For example, a Web Service that connects to the system to retrieve the data it needs to display information to the customer.
- FTP Profiles—Used to either send files to or receive files from external sites. These can also be used to FTP files between IBM i systems.
- Third-Party Application Profiles—These are usually the profiles created by the installation process of purchased third-party applications, such as those from HelpSystems or Townsend Security.
- Group Profiles—Profiles used in the Group Profile parameter of a user profile. Their purpose is generally for additional security or object ownership.
- IBM-Supplied Profiles—Profiles that are created as part of the operating system or an IBM Licensed Program. These generally start with the letter Q.
It’s a good idea to check profiles under these categories on at least a quarterly basis to make sure they are still needed. This is something that you would want to state in your policy as well. For the most part, user profiles that fall under these categories would be the exception to the 60-day policy. Note: As a general rule, I never touch or modify an IBM-supplied profile unless directed by IBM support to do so, and honestly, even then I hesitate.
We now have our list down to the profiles that are eligible to be removed. Hold on! Before we can delete them, we need to check a couple more things. First, we need to see what the user profile owns. This can be accomplished by putting a 12 next to the profile on the Work with User Profile screen (Figure 1 below).
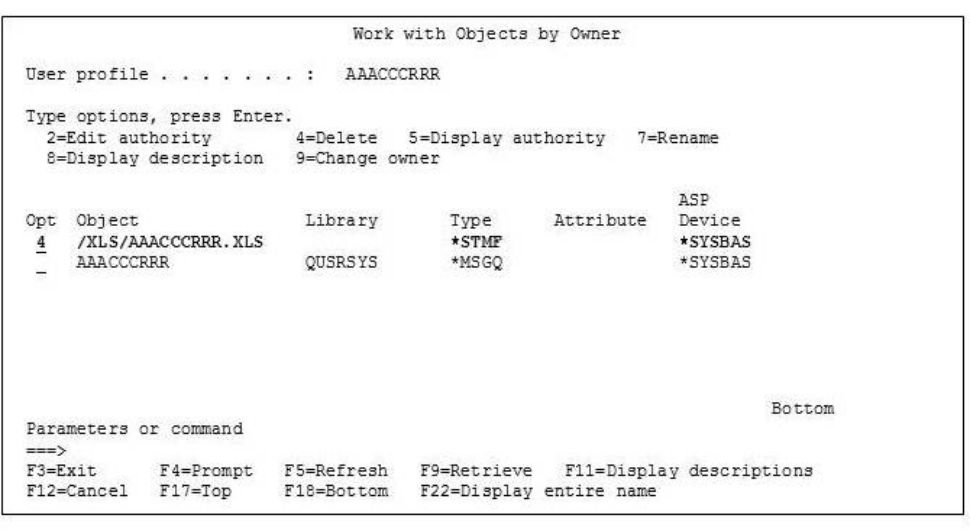
Figure 1: Use the Work with User Profile screen to see what the user profile owns.
Typically, a user who falls under the User, Developer, Help Desk, System Administrator, or Computer Operations categories should not own any objects except their message queue. However, if they do own objects, you will need to decide what profile you should transfer the ownership to. As a rule of thumb for me, it’s usually to the group profile. However, it can be to whatever profile you deem to be the best fit for the object.
The last area to check before you can delete the profile is third-party applications. Deleting a user profile will remove private authority to objects, but it will not remove the user from these types of applications. Many of these applications have their own security that you must add a user to. Having a policy and procedure for when a user needs to be added to a third-party application would be helpful in determining which applications need to be checked.
The following is a user profile deletion policy template. This template lists things that should be included in the policy. This is not an all-inclusive list; you can add, remove, or modify as it applies to your environment. Also remember that you should have procedures for each action item on the list. When performing an audit, an auditor will most likely look to both the policy and the procedure.
User Profile Deletion Policy Template
1. Policy purpose statement
2. Termination report from Human Resources—From this list, you can disable the user profile associated with the terminated employee.
3. Determine how long a profile must be out of use to qualify for removal—Two date parameters to look at: Previous Sign-On date and Last Used date.
4. Determine the type of profile.
- User
- Help Desk
- Computer Operations
- Developer
- System Administrators
- Service Profiles
- FTP Profiles
- Group Profile
- Third-Party Application Profiles
- IBM-Supplied Profiles
5. Object ownership—Determine which profile the ownership of objects should be transferred to.
6. Third-party application—Remove a user from third-party application security.
7. Exception list—Define what is excluded from policy and why
8. Modification list—This section details when a modification to the policy was done and by whom.
9. Manager/executive signoff—Someone needs to own the policy. These types of policies need to be known throughout the company, so it helps if there is a policy owner (usually the department manager or an executive). Signoff should be required whenever the policy comes up for review, usually annually.
OK, you have followed your policy and performed the necessary checks. Now you are ready to delete the unused user profiles. Easy enough: Just put a 4 next to it and hit Enter (you will have to hit Enter again to confirm the deletion). Poof! The profile is gone. Your sock drawer is once again in a manageable state.


















 More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment.
More than ever, there is a demand for IT to deliver innovation. Your IBM i has been an essential part of your business operations for years. However, your organization may struggle to maintain the current system and implement new projects. The thousands of customers we've worked with and surveyed state that expectations regarding the digital footprint and vision of the company are not aligned with the current IT environment. TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now.
TRY the one package that solves all your document design and printing challenges on all your platforms. Produce bar code labels, electronic forms, ad hoc reports, and RFID tags – without programming! MarkMagic is the only document design and print solution that combines report writing, WYSIWYG label and forms design, and conditional printing in one integrated product. Make sure your data survives when catastrophe hits. Request your trial now! Request Now. Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works.
Forms of ransomware has been around for over 30 years, and with more and more organizations suffering attacks each year, it continues to endure. What has made ransomware such a durable threat and what is the best way to combat it? In order to prevent ransomware, organizations must first understand how it works. Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include:
Disaster protection is vital to every business. Yet, it often consists of patched together procedures that are prone to error. From automatic backups to data encryption to media management, Robot automates the routine (yet often complex) tasks of iSeries backup and recovery, saving you time and money and making the process safer and more reliable. Automate your backups with the Robot Backup and Recovery Solution. Key features include: Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online