Are IBM profiles making your system vulnerable?
When performing an audit on IBM i, a common concern is identifying and auditing IBM profiles. Depending on your software makeup and configuration, IBM will install no fewer than 20 (and possibly 50 or more) user IDs on your system in support of the operating system and licensed program products (LPPs). From an auditing and compliance perspective, you need to ask yourself some questions:
- How are these IDs protected?
- Could these IDs be compromised?
- How can I tell legitimate IBM profiles from imposters?
Bare-knuckled IBM i programmers may have the time to yank the answers to these questions directly out of the operating system--and may even enjoy the challenge--but resourceful professionals will want to have the information presented to them in an easily understood and easily distributed format. In this article, I'll explain both approaches.
Every IBM profile carries a certain amount of power. Some, like QSECOFR, are all-powerful. Others, like QTCP, are also powerful because they are the profiles IBM uses to run certain system utilities. The good news is that only three IBM profiles might ever actually require a password. We know QSECOFR must have a password because it is the profile of last resort; if all else fails, this is the profile that you will need to sign on and correct a system problem. QSRV and/or QSRVBAS might be used on occasion by IBM hardware service personnel, but on a day-to-day basis, they should have their passwords set to *NONE. All other IBM-supplied user IDs can have their passwords set to *NONE without negatively impacting operating system functions. Completing these simple steps is the first big step toward protecting your system from rogue uses of IBM profiles.
The next step requires finding out if these IDs are protected from profile hijacking. To know whether these IDs are protected, you need to investigate two elements of the user profile: the last signon information and the object authorities to the user profile object itself. Last signon information will tell you if this user ID has been used recently, and the object authorities will tell you whether the profile could be hijacked by some other user.
For the bare-knuckled crowd, you'll want to start by dumping all user profile objects into an outfile using the DSPUSRPRF command. Because all IBM profile names begin with the letter Q, you can limit your queries to just this group of users. Once those IDs are isolated, you'll want to query that outfile. Specifically, you'll want to look at the "System Created on" field. For most IBM profiles, the System Created on is '00000000'. If the "System Created on" is your system name, you'll want to dig down a level to see if this ID is legitimate. Because some IBM user IDs, such as QLPINSTALL, are legitimately created on your system, you will need to investigate surrounding issues, such as object creation date (does it coincide with the operating system install or an LPP load date?) and the "Created by User" (is it QSECOFR or FSMITH?). Remember that not every user ID that starts with the letter Q is necessarily an IBM profile, so you'll have to investigate and justify each one.
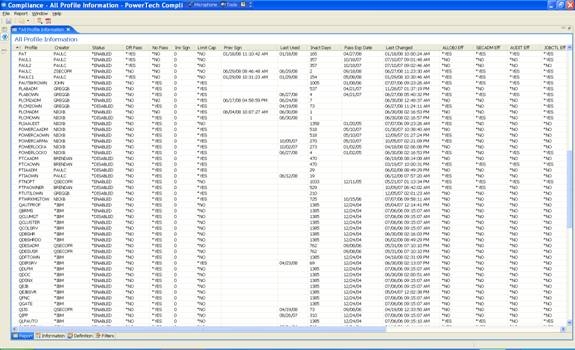
For a less-complicated solution, take a look at PowerTech Compliance Monitor software. Compliance Monitor provides a single report that you can run that will list all user profiles (Figure 1).
Figure 1: Compliance Monitor lists all profiles on a system. (Click images to enlarge.)
Compliance Monitor also includes a handy filter that allows you to filter in (or out) all of the IBM-supplied profiles that are shipped with the operating system or LPPs (Figures 2 and 3).
Figure 2: Apply a filter to isolate bona fide IBM profiles.
Figure 3: List only the IBM profiles.
Isolating IBM-supplied profiles is easy now because Compliance Monitor already knows what you are looking for. This is just one of thousands of customizable reports that you can glean out of PowerTech Compliance Monitor in just a matter of seconds.
So whether you are a grizzled old IBM i person or an enterprise security specialist with no IBM i knowledge, PowerTech Compliance Monitor helps you to check your system's compliance to your own security standards quickly and easily.














 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online