PowerTech's annual "State of IBM i Security" study tells a scary story.
Back in the dark shadows of days of old, strong security controls provided a ring of protection around IBM i information. While the majority of these controls date back to a time when the server was still known as the AS/400, it's scary how many shops still aren't using them.
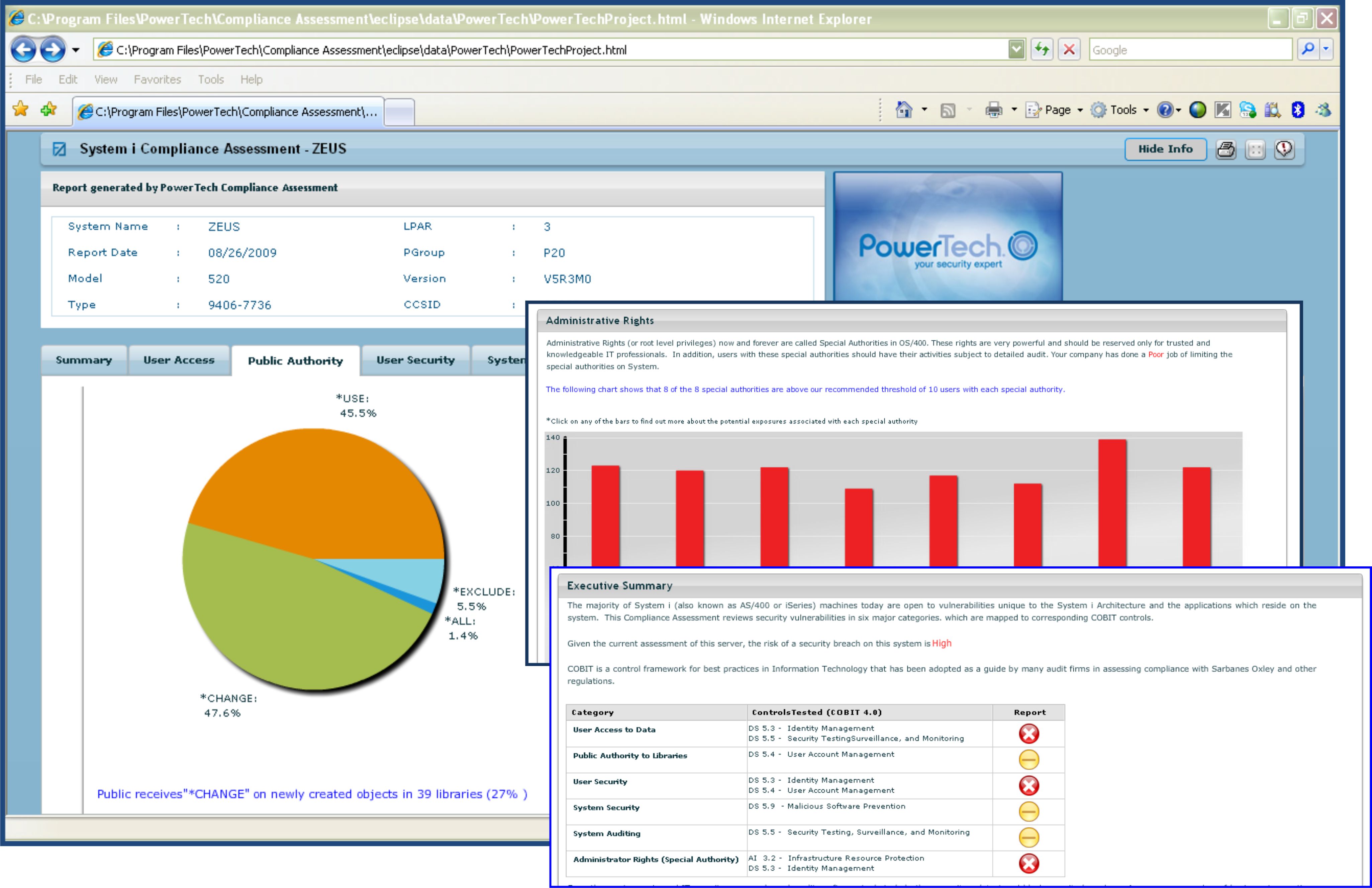
PowerTech performs more than 200 Compliance Assessments each year as a service to IBM i organizations, and the collected data is used in our annual "State of IBM i Security" study. Unfortunately, year after year, the study shows that there's still a lot of room for improvement. Let's take a look at some of these areas.
Powerful User Profiles
Overly powerful user profiles continue to be one of the most prevalent issues. Companies assign special authorities to users without much regard for actual need and with little understanding of the capabilities that each provides. Root access (*ALLOBJ) often is granted to users who have no legitimate business need for it, including programmers and administrators on production systems. This is rarely justified, and, in fact, is a regulatory no-no. Other special authorities also continue to be granted liberally, including *JOBCTL, with its ability to end the system to a restricted state, and *SAVSYS, which allows a user to delete data from any data file object, regardless of any authority restriction.
*PUBLIC Authority
We review public authority to libraries to understand the access that's granted to anyone with a user profile and password. In 91 percent of cases, users have access rights of at least *USE, making it a simple task to access information outside the control of approved applications. Combined with overly powerful profiles, this is just another way users can view and change data.
Passwords
Security often suffers from weak password requirements. Unbelievably, we continue to see systems with a minimum password length of one, as well as no forced expiration requirements. Incorrect passwords often disable profiles after several attempts, but too many profiles have default passwords or have not been used for an extended period of time. We still see profiles that are not secured from *PUBLIC, making them available for anonymous use by any user with command-line access.
System Values
System values often are left at the IBM-shipped default. While these are the minimum recommended values, I believe this is due as much to IBM changing the default (since security level 40 finally reflects the most common settings) as it is to any conscious effort on the part of the security officer. I also feel that people place too much emphasis on the security level, since numerous other values and controls influence its effectiveness. For example, we've assessed many systems operating at security level 40 that have a large cross-section of users running with *ALLOBJ special authority, effectively rendering it the equivalent of security level 20.
Network Access
Even after more than 15 years of operating system support for exit programs to monitor and control network access, 57 percent of shops still do not have a single exit program in place. Of the 43 percent that do have exit programs, many of them do not have coverage across all of the 30-plus exit points that exist. Even organizations that use commercial exit point applications often don't maintain the rules or invest in keeping their skills—or the application—current. It's surprising how many customers still are totally unaware that several network interfaces allow users to execute system commands, regardless of green-screen command restrictions.
Auditing
Although the base operating system includes audit functions, only 82 percent of servers are actively using them. In addition, many of those shops use auditing for high availability replication rather than for security forensics. Ironically, virtually every regulation contains the directive to track user activities and to provide audit reporting of events, so it's fortunate that this is an easy area to improve.
A Treat, No Tricks
PowerTech has its porch light on and is handing out a sweet treat to readers: sign up today for a FREE Compliance Assessment and see how your environment measures up (see Figure 1). For a copy of the study that fueled this article, click here. There's no cost and no obligation for either resource; just the opportunity to avoid a terribly scary ending!
From the leader in IBM i security, Happy Halloween.
Figure 1: A PowerTech Compliance Assessment reviews your system security configuration. (Click image to enlarge.)
as/400, os/400, iseries, system i, i5/os, ibm i, power systems, 6.1, 7.1, V7,












 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online