The good folks at IBM want the iSeries to be a friendly and capable part of your Windows network. Toward that end, capabilities allowing integrated two-way data communication are built in to i5/OS (OS/400 V5R3). This is the first of a two-part series that addresses the features and configurations of iSeries NetServer and QNTC, the enabling support within i5/OS.
iSeries NetServer
NetServer is how the iSeries integrates with Windows networking. NetServer allows you to access the iSeries' disk and printers much the way you access a local resource on your PC. It is very similar to the "shared folders" functionality of the past.
Starting with V4R2, IBM simplified life for us somewhat by including Server Message Block (SMB) technology natively on the iSeries through NetServer (which is part of the iSeries operating system). Therefore, the special drivers included with iSeries Access that enabled iSeries network drive functionality no longer must be present for the iSeries to participate in the Windows network.
Windows Network Integration Advantages
If you're familiar with the shared folders support in previous versions, you'll find that the network drive support for Windows is a big improvement. The main difference is that you can access your iSeries' filing system through Windows networking without having to assign a drive letter.
If you have the proper security authority, you have access to the entire iSeries file system through the IFS. (With shared folders, you were restricted to the QDLS file system.) With network drive and Windows integration, you can access files in iSeries libraries, documents in the shared folder area, other iSeries that are sharing their filing systems, any UNIX systems sharing their files with the iSeries through NFS, and more.
Copying files back and forth between the PC and the iSeries becomes as simple as copying any other file within Windows. You can cut files and paste them onto the iSeries, you can drag files from your desktop and drop them into a folder on the iSeries (and vice versa), etc. When you copy files between the systems, they can automatically be translated from ASCII to EBCDIC or the reverse as needed.
iSeries support for Windows networking even gives you the "convenience" of being able to delete any files that you have authority to by simply highlighting the files and pressing the Delete key--like any other Windows file. (See the section on security below.)
Windows Networking Integration Disadvantages
OK, iSeries support for Windows networking is pretty cool. But let's take a look at the three main disadvantages of iSeries Windows networking integration:
Performance--Depending on your setup, speed can be an issue. However, each new release of the iSeries operating system has improved the speed.
Security--As with other client-integration tools for the iSeries, Windows integration introduces no new security holes. It merely gives point-and-click access to existing ones (which can have significant implications). The security issues introduced are the same ones present in any distributed environment.
PC overhead--Windows networking integration is part of base support of i5/OS. This means it will be installed when client support is loaded on your PCs. There is no option to not install it.
Starting NetServer
Before you can use network drives to access your iSeries, you must configure an iSeries connection. Network drives work over all iSeries connection types.
Give your NetServer server a name to run under. Start iSeries Navigator and locate the NetServer entry under Network>Servers>TCPIP. Select NetServer and right-click; then go into Properties and click the Next Start button. Specify a server name and a domain name. Note that the name specified, Qs101901r, is not the iSeries' system name. Windows networking support and standard iSeries networking support cannot coexist under the same name, so the Windows networking name is customarily appended with a "Q."
All that remains is to start the NetServer job. Select the NetServer entry again and click the Start button. (If your iSeries is not set to start support for Windows networking automatically, you will have to start the server job manually using the Navigator after each IPL.) Now, you may let your PC "discover" the iSeries server.
When you create connections within iSeries Access, each iSeries connection that you configure shows up when you select the My Network Places icon on your desktop. If you don't have an active connection to the iSeries, one will be made when you select an iSeries from within the Windows networking.
Using the Network Drive Function
To begin using the network drives function, click the Windows networking icon on the desktop. Next, click the computer icon for the iSeries you want to access. If you haven't already established a connection to that iSeries, one will be started for you automatically.
Depending on your setup, you may have to make your PC "discover" the NetServer program that's running on the iSeries. You can start any PC function that includes a browse function--like Windows Explorer--to perform the discovery. Open Network Places>Entire Network to list the connections in the network (Figure 1). The value specified here will match that specified for the iSeries' NetServer utility program as configured with the Navigator.
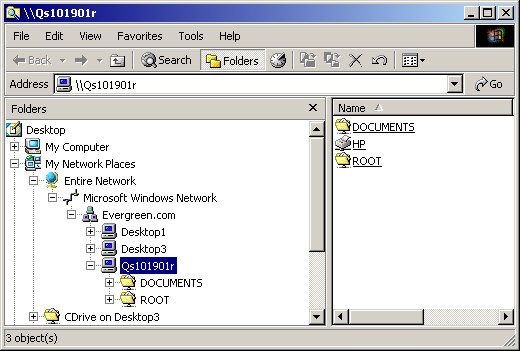
Figure 1: Specify the path to the iSeries. (Click images to enlarge.)
Once the PC-iSeries connection is established, you'll see a path to iSeries folders similar to the one shown in Figure 1. This is the highest level (the "root") of the iSeries IFS. This level represents the entire iSeries system, and it allows you to navigate to each filing system by going to the appropriate folder.
Generally, you use your connection to the iSeries to store PC files within the IFS structure, but you can also access standard iSeries objects like source physical files. The standard iSeries library filing system is located under the root as qsys.lib, and it's likely to be where most of your objects are located. Because of the large number of objects in this filing system, accessing qsys.lib can be rather slow. If you open qsys.lib, you'll see a folder for each library on your iSeries (including all of the system libraries).
Mapping a PC Drive to the iSeries
If you use network drives to access a certain area of the iSeries often, you might want to consider mapping a drive. When you do that, the drive shows up under the My Computer icon on your desktop. When you select the drive, it takes you directly to the area on the iSeries that you want.
You can map a drive by right-clicking the My Network Places icon on the desktop and selecting Map Network Drive from the menu. Specify a letter name and the path to the iSeries folder to be mapped (Figure 2).
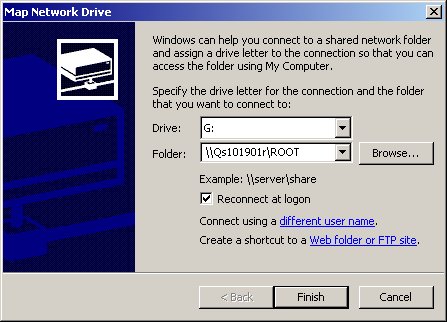
Figure 2: Map a letter drive to an iSeries folder.
From then on, you can bring up the contents of the mapped drive by selecting the drive under the My Computer icon on the desktop or the equivalent (Figure 3).
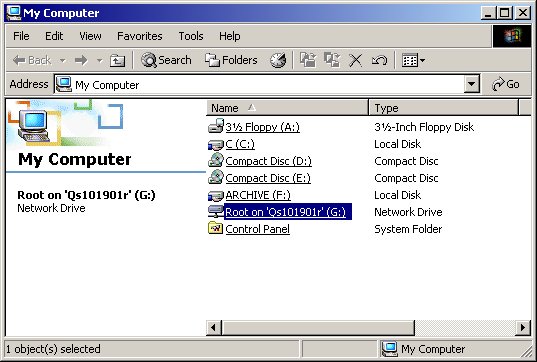
Figure 3: Your mapped iSeries drive shows up under My Computer.
NetServer Security
If network drive capability--combined with the fact that it's currently automatically installed with iSeries Access--alarms those of you responsible for your iSeries' security, it should. Gone are the days when you could secure your iSeries fairly well by simply making sure users didn't have access to a command line.
To ensure that your iSeries is safe in a networked environment, you must use iSeries resource security. While a complete discussion of iSeries security is beyond the scope of this article, there are a couple of things to keep in mind:
- The authority to objects through all client integration functions (network drives, ODBC, file transfer, etc.) is set by the profile used to make the connection. If that profile has the authority to delete a file, it can easily be done through the Windows Explorer. If the profile doesn't have that authority and the user attempts to perform the operation, the user will be denied.
- There is an authorization list with a specific name (qpwfserver) that can be used to secure access to the qsys.lib objects via the network drive function. If you create this authorization list on the iSeries, only the user profiles contained in the list will be able to access the objects in the qsys.lib filing system. However, this authorization list does not secure the other directories in the IFS. It also is an all-or-nothing proposition. It can't be used to secure portions of qsys.lib.
NetServer is a good example of the integration possible between Windows and the iSeries. In the next article, we'll go the other way: making Windows NT data available to iSeries applications, with IBM's QNTC support.
Chris Peters has 26 years of experience in the IBM midrange and PC platforms. Chris is president of Evergreen Interactive Systems, a software development firm and creators of the iSeries Report Downloader. Chris is the author of The OS/400 and Microsoft Office 2000 Integration Handbook, The AS/400 TCP/IP Handbook, AS/400 Client/Server Programming with Visual Basic, and Peer Networking on the iSeries (MC Press). He is also a nationally recognized seminar instructor. Chris can be reached at













 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online