Getting System i Access for Web up and running in your business isn't hard. Here's how!
System i Access for Web enables users to access their IBM i resources and applications through a browser interface. Users can upload PC data to DB2 for IBM i, query and download database information, start a 5250 interface, work with printer output, and more. The product is running entirely on your IBM i. The only requirement on the desktop is a browser, and no applets are running in the browser. Therefore, the product has lots of appeal for administrators: best of all, you don't have to deal with the installation and maintenance of client desktop software. The product can be used from any desktop or device that has a browser, so your users with mobile devices or Mac, Linux, or other operating systems can get at IBM i resources through the Web interface.
In this article, we will discuss the software requirements for System i Access for Web and give you some tips on configuration. Then we will take a look at how administrators can restrict access to functions for their users.
The Web-Serving Environment
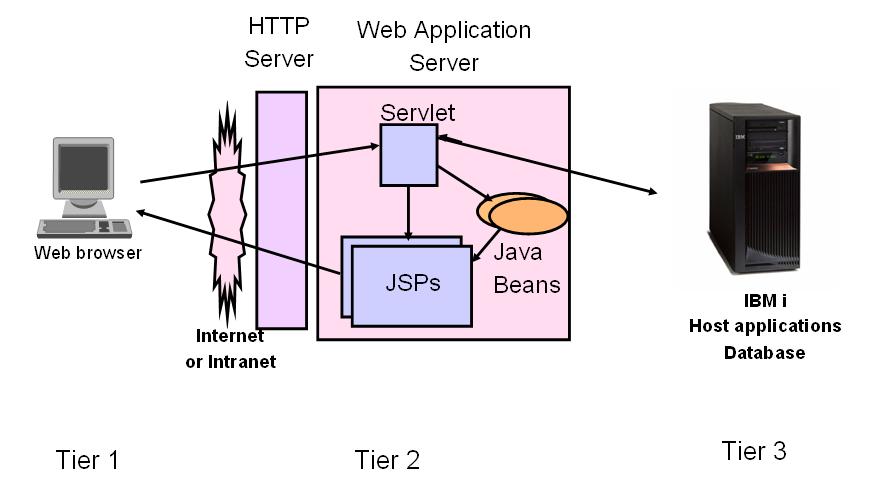
Figure 1 shows our IBM i Web-serving environment.
Figure 1: The IBM i Web Application Serving Environment (Click images to enlarge.)
Tier 1 is the end user on the browser, accessing the URL that has been configured for System i Access for Web. This user could be coming from the Internet or be within your intranet.
Tier 2 is the Web-serving environment. There are three pieces:
1. The HTTP Server is the front door into the Web-serving environment. It routes requests between the end-user browser and the Web application server. The HTTP Server is listening for requests on a specific TCP/IP port that you specify during System i Access for Web configuration.
2. The Web application server provides a Java Virtual Machine (JVM) environment where Web applications run.
3. System i Access for Web is the Web application in this case. It provides specific function that users access using their Web browser.
Tier 3 contains the IBM i resources that the users need to get at: host applications, database, printers, files in the IFS, and so on. Many of you will be running tier 2 and 3 on the same IBM i machine, but those could be on separate machines or partitions.
Client Requirements
What is required for tier 1? The only requirement on your desktop or mobile device is a browser. The product has been tested with recent versions of Internet Explorer on the Windows desktop; Firefox and Opera on Windows and Linux; and Mozilla on Windows, Linux, and AIX. Since the product is not running applets in the browser, other browsers that support the current HTTP and HTML specifications should work.
Required IBM i Software
Let's look at the software requirements for tiers 2 and 3. This article refers to the currently available releases, V5R4 and V6R1. Be aware that System i Access for Web was available starting in V5R1 i5/OS, so if your system has an earlier release than the releases listed here but is at V5R1 or later, you have the product.
IBM i software requirements (57xx refers to 5722 or 5761):
- IBM i V5R4 or V6R1 (57xx-SS1)
- 57xx-SS1 option 30: Qshell Interpreter
- 57xx-SS1 option 3: Extended Base Directory Support
- 57xx-SS1 option 8: AFP Compatibility Fonts, if you plan to convert spooled files to PDF
- 57xx-SS1 option 34: Digital Certificate Manager, if you plan to use SSL
- 57xx-SS1 option 35: Cryptographic Service Provider, if you plan to use SSL
- TCP/IP Connectivity Utilities for AS/400 (57xx-TC1)
- Developer Kit for Java (57xx-JV1). Check the WebSphere or the integrated Web application server documentation to see which 57xx-JV1 option you need for your Web application server of choice.
- IBM Toolbox for Java (57xx-JC1)
- IBM HTTP Server (57xx-DG1)
- System i Access Family (57xx-XW1). Family licenses are required in order to use the function in System i Access for Web.
- System i Access for Web (57xx-XH2)
- Optional: Infoprint Server for iSeries (5722-IP1)
- Choose a Web application server. The next section will cover the Web-serving environments that are supported with System i Access for Web.
V5R4 System i Access for Web installs on V5R3 and V5R4 IBM i, and V6R1 System i Access for Web installs on V5R4 and V6R1 IBM i. Eligible customers who want to keep their operating system at V5R4 and acquire the V6R1 System i Access Family of products--both Web and Windows--can do so by ordering feature 2649 of 5722-XW1. In order to be eligible, customers must be System i Access Family customers and have software maintenance.
Supported Web-Serving Environments
System i Access for Web servlet code can be used with any of the following Web application servers:
V6R1 System i Access for Web
•· Integrated Web application server: part of IBM HTTP Server for i, 5761-DG1
•· WebSphere Application Server (WAS) V6.1 and V6.0 - Express for i5/OS
•· WAS V6.1 and 6.0 Base and Network Deployment
Note: V6R1 System i Access for Web support of WAS V7.0 will be available in the first quarter of 2009. The support info will be added here.
V5R4 System i Access for Web
•· Integrated Web application server: part of HTTP Server for i, 5722-DG1
•· WAS V6.1 and V6.0 - Express for i5/OS
•· WAS V6.1 and 6.0 Base and Network Deployment
•· WAS V5.1 and 5.0 - Express for iSeries
•· WAS V5.1 and 5.0 Base and Network Deployment Editions
•· ASF Tomcat: part of HTTP Server, 5722-DG1. V5R4 is the last release to support Tomcat.
Note: There are currently no plans to support V5R4 System i Access for Web with WAS 7.0.
System i Access for Web also has portlets that are supported with several of the portal servers available on IBM i. Contact me via email (in my bio at the end of the article) if you need more information about our portlets.
Port Requirements
An advantage of having the System i Access for Web product running entirely in servlets is that you need only one port open in your firewall for the product. Figure 2 shows a comparison of port requirements for a client-server application like System i Access for Windows with System i Access for Web.
Figure 2: Comparison of Port Requirements for Windows and Web Products
A disadvantage with client-server applications is having to open many ports for specific functions, as shown in the list for the Windows client. Many of you don't want to open the Telnet port. For System i Access for Web, you need only one port open. If you are not configuring your HTTP Server for SSL, port 80 is the default; alternatively, you can specify any open port during configuration. If you are configuring your HTTP Server to use SSL, port 443 is the default, or specify any open port.
Performance Considerations
Many of you ask, "How does running System i Access for Web affect the performance on my system?" The product by itself does not levy a lot of additional processor and memory requirements on the system. However, you will need to determine whether the Web application serving environment will affect your overall system performance. For WAS, use the IBM Systems Workload Estimator to size your system configuration. Although the tool does not list the System i Access for Web product as a workload to size, you can select the HATS or WebFacing options to get a comparable estimate. For performance considerations for the integrated Web application server, refer to the FAQ Web page.
Configuration: Integrated Web Application Server
What is the integrated Web application server for i? This is a lightweight Java application server integrated into the operating system. It first became available on V5R3 i5/OS. In this article, I'll refer to the V5R4 and V6R1 versions. Similar to the ASF Tomcat server, it uses fewer system resources than WAS and requires minimal effort for an administrator to maintain. Some of you have systems that are not powerful enough to run WAS. In the past, we've recommended that you try the Tomcat server. Since V5R4 is the last release to support Tomcat, the integrated Web application server is an alternative.
How is it packaged? The integrated Web application server is part of the HTTP Server licensed program (57xx-DG1) with V6R1 and V5R4, delivered with group PTFs. Since HTTP Server automatically comes with the IBM i operating system at no additional charge, everyone has it. Refer to the Web page for the group PTFs and any other PTFs needed.
In addition to being able to create your own instances, the integrated Web application server provides an administrative instance with a preconfigured HTTP Server specifically for System i Access for Web. V5R4 System i Access for Web supports only the Administrative instance. V6R1 System i Access for Web supports both the Administrative instance and user-created instances.
Let's look at how to configure each of these.
Administrative Instance and Preconfigured HTTP Web Server
Using V5R4 or V6R1 System i Access for Web:
1. Stop the Web Administration for i5/OS:
ENDTCPSVR SERVER(*HTTP) HTTPSVR(ADMIN)
2. Load/apply latest PTFs (review cover letters for any additional information):
For V6R1: SF99115 group PTF for 5761-DG1, level 1 or later
For V5R4: SF99114 group PTF for 5722-DG1, level 13 or later
3. Load/apply the latest System i Access for Web PTF:
For V6R1: SI29664 or later
For V5R4: SI29607 or later
4. Configure System i Access for Web. From a 5250 command line:
QSH
cd /QIBM/ProdData/Access/Web2/install
cfgaccweb2 -appsvrtype *INTAPPSVR
5. Start the Web Administration for i5/OS:
STRTCPSVR SERVER(*HTTP) HTTPSVR(*ADMIN)
6. Start the preconfigured HTTP web server:
STRTCPSVR SERVER(*HTTP) HTTPSVR(IWADFT)
7. Open a browser to System i Access for Web using the preconfigured HTTP port. Note that you didn't have to specify the port in the configuration. 2020 is the default port for this administrative instance. Key in the following URL, where is replaced with the name by which your system is known on the network: http://:2020/webaccess/iWAMain
You should see the System i Access for Web main page!
User-Created Instance and HTTP Web Server
V6R1 System i Access for Web is the only release that supports the user-created instance. Recall that you can run V6R1 System i Access for Web on either V5R4 or V6R1 IBM i.
1. Load/apply the latest PTFs (review cover letters for any additional information):
For V6R1: SF99115 group for 5761-DG1, level 1 or later
For V5R4: SF99114 group for 5722-DG1, level 13 or later
2. Load/apply the latest V6R1 System i Access for Web PTF:
V6R1 SI29664 or later
3. Start the Web Administration for i5/OS:
STRTCPSVR SERVER(*HTTP) HTTPSVR(*ADMIN)
4. Use the Web Administration for i5/OS wizard to create an instance of the integrated Web application server and an HTTP web server:
http://:2001/HTTPAdmin
Click here for the step-by-step instructions if you need help with the wizard.
5. Configure System i Access for Web. From a 5250 command line, type this:
QSH
cd /QIBM/ProdData/Access/Web2/install
cfgaccweb2 -appsvrtype *INTAPPSVR -instance
Replace with the name you specified in the creation wizard in step 4.
6. Start the integrated Web application server and HTTP web server using the Web Administration for i5/OS interface:
http://:2001/HTTPAdmin
7. Open a browser to System i Access for Web using the HTTP port:
http://:
Replace with your system and
I've summarized the instructions for configuring the integrated Web application server. Every V5R4 and V6R1 IBM i has this software with the group PTFs, it requires fewer system resources than the WAS servers, and it is very straightforward to configure. Once the necessary PTFs are applied, you can get System i Access for Web configured in a few minutes.
WebSphere Application Servers
Some of you are already using WAS, or you are using other Web applications in your business that require WAS. If you need more information about why you might use WAS rather than the integrated Web application server, contact me.
As for configuring System i Access for Web in WAS environments, the configuration of WAS - Express and the WAS Base editions is done using the Web Administration wizard, using many of the same steps as for the user-created instance of the integrated Web application server. For step-by-step instructions for these or for any of the supported web application servers, refer to the Information Center. Start here and then select your i release. Once at the Information Center home page of your release, navigate to "Connecting to System i" and then "System i Access" (or "iSeries Access" for earlier releases) to find System i Access for Web.
So far we've looked at the prerequisite software and configuration information for System i Access for Web. Next, here is an introduction to how administrators can restrict access to functions for their users.
Setting Policies
After configuration, the next area of System i Access for Web that administrators need to be familiar with is the Policies function. Realize that if you have your objects secured on your system, your end users will not be able to access them using System i Access for Web. However, it is likely that you want to limit the options that your users see in the interface. Policies are the mechanism by which administrators control access to the product's functions. Policy settings can be administered at the IBM i user and group profile level. In order to customize policies, the administrator's user profile must have *SECADM special authority. Additionally, a user with *SECADM authority can set a policy called "Grant administrator privileges" to allow another user profile to edit System i Access for Web policy settings.
System i Access for Web enforces policy settings for a user in the following order:
1. If a policy has been specifically set at the user profile level, it takes priority over all other settings.
2. If no policy has been set at the user profile level, then group profile memberships are checked, where the policies are aggregated across group memberships. If the policy has been set for any of the user's group profiles, it is enforced.
3. If no policy has been set at either the user or the group profile level, then a special group called *PUBLIC is checked. *PUBLIC is a group profile that is created by System i Access for Web, where all System i Access for Web users are automatically members of this group and cannot be removed from it. A policy that has been set in this *PUBLIC group profile is enforced if none have been set at the user or another group profile level. If a policy setting has not been changed, then the shipped default policy setting for the *PUBLIC group profile is enforced.
Removing Unwanted Functions from the Navigation Menu
By default, most policies are set to allow all users access to the System i Access for Web functions. Figure 3 shows the default navigation menu that appears on the left side of the screens. These are the out-of-box functions available to System i Access for Web users.
Figure 3: System i Access for Web Home Page with Default Left Navigation Options
Let's look at an example of how to restrict functions. Suppose we have a group profile called SALESGROUP, and the only function we want users in this group to see are their invoices, i.e. printer output, and no other functions. The printer output function shows the authenticated user's IBM i spooled files, so it is comparable to running Work Spooled File (WRKSPLF) from a command line.
The first thing to do is eliminate all the options on the menu that you do not want users to access. Edit the policies for the SALESGROUP and deny access to the other capabilities. Figure 4 shows that I am the administrator, LLHIRSCH, signed onto System i Access for Web.
Figure 4: Customize Policies for Group Profile SALESGROUP
On the left navigation menu, take Customize > Policies. For the prompt, "Specify the user profile you want to edit," enter the SALESGROUP profile, and press Edit Policies. Figure 5 is the result.
Figure 5: Categories of Policies That Can Be Changed
Here are the categories of functions for which you can set policies. Printer output is in the "Print" category. We want to deny access to all categories except Print. Start by clicking the edit icon in the Action column for the top category, 5250. As shown in Figure 6, go to the top level to the policy called "5250 access" and change the default Allow to Deny. Scroll down and press the Save button.
Figure 6: Deny Access to the 5250 Category of Function
When a function is set to Deny, its navigation menu content is not displayed and access to the corresponding function is restricted. Users cannot access the function from System i Access for Web by any method, e.g., entering the URL to get directly to a function.
Next, go into all other categories other than Print and change the top-level policy in each from Allow to Deny. You skip the General category, since this category is for things like modifying page layout and for specifying the home and templates pages, which are not functional categories.
Once these steps are complete, then when SALESMAN, a member of the SALESGROUP, signs on to System i Access for Web, the left navigation menu is reduced to the single category "Print," as shown in Figure 7.
Figure 7: Left navigation Has Reduced Function but Print Subcategory Needs to Be Reduced
When SALESMAN clicks on the Print category, the default subcategory functions are also shown in Figure 7. Suppose there are many of these functions that we don't want the sales group to access: e.g., working with printers, output queues, and so on. We want to reduce the subcategories to only "Printer Output."
To do this, go back on the LLHIRSCH administrator's browser (Figure 5), and from the Customize > Policies function for SALESGROUP, edit the Print category. Leave the top level "Print Access" and "Printer Output" subcategory settings as Allow. Scroll through the Print section and change all other subcategories to Deny: PDF Printer Output, Printers, PDF Printers, Internet Printers, and so on. Press the Save button.
Now the result in SALESMAN's browser when SALESMAN selects the "Print" tab is in Figure 8. Instead of the long list of Print subfunctions we saw in Figure 7, the only one showing is "Printer output". SALESMAN clicks on this to see his Printer output.


















 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online