DB2 for I 7.2 delivers a feature that can increase the integrity of your database.
With the intense focus on data privacy, many applications are being modified to protect the personal data that they are processing. Masking is a data protection technique that's commonly being deployed so that the vast majority of application users are allowed to see only a masked version (############1234) of sensitive data values, such as credit card numbers. Access to the original card number value is limited to a select set of privileged users.
This masking can be implemented with application logic or by using a built-in database feature such as the column mask support just delivered with DB2 for i 7.2 release. The following mask definition ensures that only application users belonging to the ADMIN group profile will be allowed to see the actual credit card number value. DB2 will automatically return a masked version of the card number for all users who don't belong to the ADMIN group profile.
CREATE MASK credit_mask ON customers FOR
COLUMN card_number RETURN
CASE
WHEN
VERIFY_GROUP_FOR_USER(SESSION_USER, 'ADMIN') = 1
THEN card_number
ELSE
'************' || SUBSTR(card_number, 13, 4)
END ENABLE
Masking logic usually works seamlessly for read operations, but caution must be exercised with programs that perform update operations. This scrutiny is necessary because the masked values from a read operation are most likely stored in application variables and buffers, and these variables and buffers can be easily passed on update operations. If this occurs, the original data value can be accidentally overwritten with a masked value.
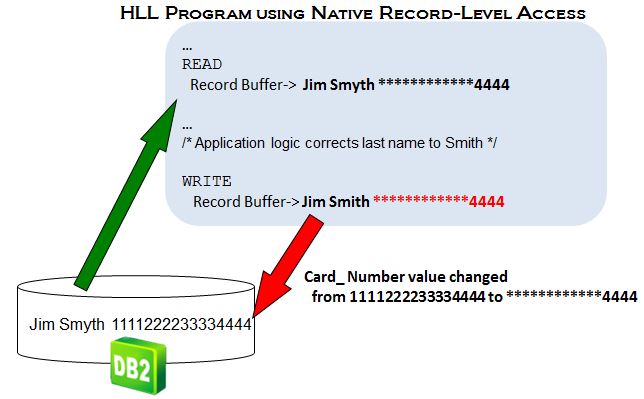
Consider a table containing three columns—first name, last name, and credit card number—that is read by an RPG program. The user running the program isn't authorized to see the card number value, so a masked value (************4444) is written into the program's record buffer as shown in the following figure.
Figure 1: A masked value (************4444) is written into the program's record buffer.
In this example, the application read the data for update in order to correct the misspelling of the last name. The last name value is changed to Smith in the buffer. Now a WRITE request is issued by the program, which uses the contents of the record buffer to update the row in the underlying DB2 table. Unfortunately, the record buffer still contains a masked value for the card number at this point, so the credit card number value in the table is accidentally set to the masked value.
To help protect against these accidental updates with masked values, the DB2 for i 7.2 release delivers enhanced check-constraint support. Check constraints can be defined to ensure that a column is assigned a set of defined values. For example, a check constraint can be defined to guarantee that a gender column contains only the values of M or F.
In past releases, if DB2 detected a value not allowed by the check constraint definition, then a hard error would be signaled, causing the associated insert or update operation to fail. While this signaling of the error prevents accidental updates with masked values, it also causes the valid part (Smyth to Smith) of the update operation to fail.
As a result, DB2 added a new clause, ON UPDATE VIOLATION, which enables the original data value to be preserved instead of an error being signaled. The following check-constraint definition prevents masked values from being assigned to the card number column by validating whether the first 12 characters match the masking character of '*'. The ON UPDATE VIOLATION clause directs DB2 to use the existing card number value (PRESERVE card_number) instead of signaling an error.
ALTER TABLE customers
ADD CONSTRAINT detect_card_mask
CHECK(SUBSTR(card_number,1,12) <> '************')
ON UPDATE VIOLATION PRESERVE card_number
This new check constraint support is not limited to usage with DB2 column masks. If your application uses program logic for data masking, the new check constraint support can also be used in that environment to watch out for masked values on update. In fact, this new check-constraint support isn't limited to masking either, so if you have a different scenario that would benefit from this new support, then that's great too!
For more information on these DB2 for i 7.2 enhancements and others, you can reference the DB2 7.2 overview presentation and the IBM i Knowledge Center. You'll need to upgrade your systems to the IBM i 7.2 release in order for these great DB2 features to increase your data privacy and integrity, so don't delay!












 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online