In essence, the intent of the regulations is to protect data integrity, confidentiality, and accountability. For instance, companies need to protect shareholders, consumers, and patients from financial misstatements and disclosure of personal information. Affected organizations must also safeguard the data they hold, such as patient histories, consumer demographics, and credit card numbers from being tainted, stolen, or maliciously modified. With the pervasiveness of data use today, protecting corporate assets can be quite a daunting task for the CISO, who is ultimately responsible for the company security plan. The details and implementation of that plan, however, are often delegated to the IT manager.
Besides satisfying mandated regulations, corporations are eager to protect their information assets because a data breach can be expensive and can tarnish a company's image. We know from the media frenzy created by data exposures that the cost to an organization can easily run into millions of dollars. The actual cost is a function of many factors, including fines, lawsuits, and lost employee productivity in the form of time spent investigating how the breach occurred and then beefing up security measures to prevent another occurrence.
To make matters worse, imagine the potential impact on customer retention, not to mention new customer opportunities, that a hit on the company's reputation could have. Although these costs are hard to measure, they conceivably could have a disastrous effect on a business.
As a CISO or IT manager, you probably feel that data security issues are getting out of control—threats to your data are increasing, government oversight is increasing, the demands of executive management for accountability are increasing, and you may feel like a pressure cooker waiting to blow. What can be done, and where can we start?
Automated Software Tools
The first step in solving this messy problem is to turn to automated software tools. Some regulated companies have already begun to recognize the benefits of automating the manual processes they put in place for compliance reasons. Purely from a cost perspective, internal labor and/or hired consultants can comprise a large portion of total compliance and data protection expense. Add to that the fact that human beings are error-prone, particularly when subject to fatigue, stress, and distraction, and companies are realizing that they are neither getting consistent value for their money nor obtaining the level of protection they need.
Although technology solutions, in the form of automated tools, do require an up-front investment, they more than pay for themselves over time in reduced labor costs. They also provide consistent, accurate, and reliable monitoring and reporting of implemented processes. Adoption of tools clearly enables a company to use its staff in a more productive way by reallocating time to higher-value business activities.
Finally, another advantage of automated tools is that they are able to work around the clock, keeping an eye on your security strategy and information assets while you sleep. Tools with real-time capabilities can even send alerts to your cell phone or pager to awaken you if a significant deviation from your security policy occurs.
If the objective is to protect corporate assets, what types of automated software tools fit the bill?
Data Monitoring Tools
There are many data monitoring tools on the market today, so let's look at the major features you should consider. To begin, think about the kinds of questions surrounding data access that you may have to answer, such as the following:
- What files did the DBA modify this week?
- What user deleted records from the PAYMENTS file?
- What changes were made to the INVOICE table last night?
- What fields were changed in the ORDER_PROCESSING file last quarter?
- Were there any changes to the PRICING file last month?
In order to answer the questions posed above, you need a tool that is continuously monitoring the critical data files you define on whatever platforms are pertinent to you. Keep in mind that there is no need to watch every file—only those that contain sensitive information or data that would significantly impact your business if compromised.
Once you've identified the files of interest, you might want a tool that lets you specify which particular fields within the files you want to audit. Or perhaps you're only interested in auditing specific users or groups. A selective approach of this nature enables you to filter out less-relevant information. Keep in mind that it's really important to strike the right balance between too much information and too little. Quality of information prevails over quantity any day of the week.
What else is important? Well, depending on your situation, you may even want to look for a tool that allows you to store the collected audit data on a different, perhaps more secure, system than the one on which your critical files reside. More sophisticated tools even let you store the audit data in a different database from the one you are monitoring. This might be a factor if you need to consider the cost of disk space. For example, monitor DB2 files and store the audit data on a Microsoft SQL server.
As you evaluate tools, remember to ask about performance impact. You certainly don't want a software tool that's going to drag your system down; you probably have enough of those applications already.
It's important to emphasize that a key feature of a monitoring tool is the ability to notify you in real time if a suspicious event takes place. Combined with real-time alerts, continuous monitoring allows you to identify exceptions as they occur—before they propagate, when they are easiest to fix and cause the least damage to your organization.
As shown in Figure 1 below, there are also tools on the market that allow you to execute predefined actions when a suspicious event occurs.
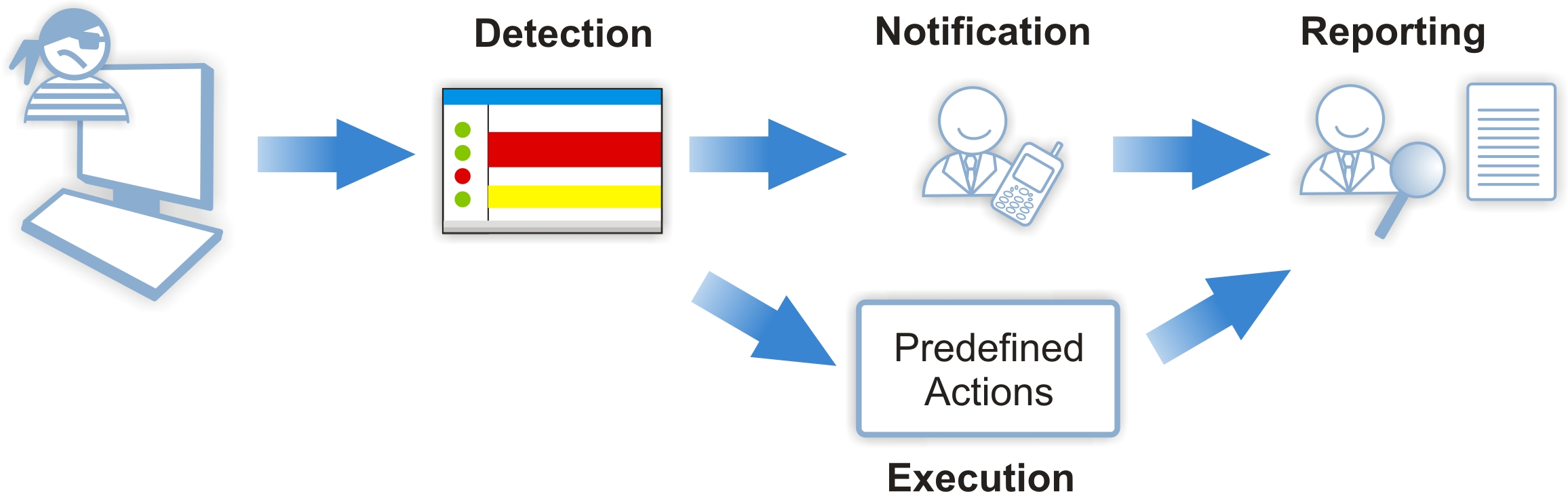
Figure 1: This diagram summarizes the desired features found in a data-monitoring tool.
For example, as you receive an alert that someone is accessing your invoice processing files after hours, you may want to run a command to disable that particular user profile to prevent further action until you figure out what's going on.
Another item on your wish list should be a tool that provides you with a variety of configurable reports so you can perform a forensic analysis of file access. For each file you choose to report on, you should be able to see the type of access (read, update, insert, delete, etc.), the date and time of the access, the user who performed the access, and even the "before" and "after" images of the data record if it changed. With this capability, you will have complete visibility over who updates sensitive tables and how—even at the field level.
If you're concerned about exposing the value of sensitive fields in a report, then be sure to require that your data-monitoring tool is capable of obscuring values on output. In other words, the actual changes in values are collected but not shown in the printed reports. See Figure 2 for a sample report segment.

Figure 2: This is a sample report segment showing restricted fields.
I also suggest that you try to find a tool that can generate reports in various formats (e.g. .pdf, .xls, .doc) so you can more easily manipulate and analyze the information. On top of that, look for a tool that can email reports to designated management for easy access.
As an added bonus, some data monitoring tools collect selective audit information in their own database, which allows you to produce reports even if the journal files are not online. Other tools offer the capability of "enriching" the audit data so an account number may appear as a customer name, for instance, thereby making the reports much easier to read. Some tools even include information in the reports about attributes not stored in the journal data, such as user class, user group, or accounting code.
Last but not least, premiere tools will have the ability to present the auditing results in a graphical way to either a PC console or a Web portal. This kind of sophistication enables the CISO and/or IT manager to identify exceptions at a glance as they carry out their daily activities.
As you can see, there are many features to consider when evaluating a data-monitoring tool. The trick is to find the best fit for your company. Even if you don't make use of every feature from the initial installation, choose a tool that will allow you to grow with it so that you are continually refining your data protection strategy.
In a Nutshell
If you haven't already implemented a data-monitoring software tool, don't wait a minute longer. The threats to your information assets are wide and varied. It's clear that you, the CISO or IT manager, can't enforce a dragnet all alone; automated tools are an essential part of the solution. So start your search and find a tool that will help you keep your corporate data and company reputation intact.
Sandy King is a Senior Consultant for the Tango/04 Computing Group. Sandy has been involved in IT for more than 25 years as a consultant, educator, and project manager. For the past 15 years, she has specialized in iSeries security. Tango/04 is a leading developer of security, system management, and automation software to help companies maintain the operating health and security of their business processes and data through intelligent management of their IT infrastructure.











 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online