New database monitoring capability gives system managers a detailed level of insight for audit-friendly "proof" and real-time alerts.
QMessage Monitor (QMM), a real-time message monitoring and escalation solution for IBM i environments, now offers a new database monitoring feature to identify real-time access issues on the system. Available now within the latest V7 release of QMM and developed by IBM i systems management experts CCSS, database monitoring will provide the system generated "proof positive" accountability auditors and IT managers require to take action against malevolent system intruders.
QMM users already have the ability to monitor the Audit Journal for real-time security breaches, but the new database monitoring capability gives them a more detailed level of insight. Now audit-friendly proof can be obtained showing not only who is accessing the system, but from where and crucially, what that person is doing with the files that have been accessed. Keeping database server activity under real-time scrutiny, IT managers can be alerted to potential security violations relating to files on libraries that contain sensitive data. The new monitor will issue a real-time message for escalation at each instance of a sensitive file being opened (read, written, deleted or updated); instances of SQL access performed through the database server (DBS) and finally, instances of native access (such as creating, deleting and retrieving information).
“IT managers and auditors will appreciate the precision the new database monitor offers,” says Paul Ratchford, product manager for CCSS. “There’s tremendous value in being able to pinpoint the exact files, libraries, users and IP addresses they are interested in–it’s a very inclusive approach to monitoring and those environments that have visibility of these issues can better protect the types of sensitive files that are sometimes targeted causing great disruption–be it those containing payroll information or personal employee details. Suspicious activity has no place to hide on the system.”
In addition to the actions associated with a file being opened as mentioned already, a manager may choose to log any or all of the following actions: creation, deletion, overriding or retrieval of file information; the reading, adding, updating or deleting of records; the adding, clearing or removal of file members and finally, when a library list is set. These rules can be applied to either specified or all users, files, libraries, library owners, programs or program libraries on the system. Database server parameters can be set using a command that allows the user to pause/restart database monitoring, either locally, if on a remote system, or for a remote system if running from the central system.
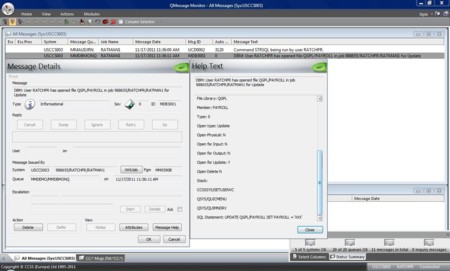
With database monitoring in place, any breach of the defined rules that occurs will be identified in real-time and escalated for immediate attention of the IT Manager or other authorized person. For example, if an unauthorized user were to select all the records in a payroll file, the alert message details include the user, action, file details and job details for an instant summary of the breach. Help text provides further details on the parameters and rules associated with the user and their client list including the top 3 programs in the call stack, and the SQL command actually run when SQL access is being used. This instant view not only provides confirmation of the breach but also saves investigation time in identifying vulnerable access points and the methods used to exploit those vulnerabilities.
For more information about QMessage Monitor please visit: http://www.ccssltd.com/products/qmessage-monitor/












 Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new.
Business users want new applications now. Market and regulatory pressures require faster application updates and delivery into production. Your IBM i developers may be approaching retirement, and you see no sure way to fill their positions with experienced developers. In addition, you may be caught between maintaining your existing applications and the uncertainty of moving to something new. IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
IT managers hoping to find new IBM i talent are discovering that the pool of experienced RPG programmers and operators or administrators with intimate knowledge of the operating system and the applications that run on it is small. This begs the question: How will you manage the platform that supports such a big part of your business? This guide offers strategies and software suggestions to help you plan IT staffing and resources and smooth the transition after your AS/400 talent retires. Read on to learn:
LATEST COMMENTS
MC Press Online